The Massachusetts Library Association (MLA) annual conference was yesterday and today in Framingham. I got to attend yesterday, and it was a full day of speakers, presentations, vendors, and catching up with library colleagues from around the state. The last MLA conference I attended was in 2019; I presented with two other librarians about DIY usability testing on library websites. (It seems like much, much longer than five years ago.)
First up, at 8:15am: “Expanding Literary Horizons: Hosting a Reading Challenge to Foster Diverse Reading Habits,” with Karolina Zapal (Massachusetts Center for the Book), Veronica Koven-Matasy (Boston Public Library), and Hannah Bernhard (UMass)
- The UMass summer reading challenge began in 2020 as a way to build community and connection while students were at home. Hannah, with the office of Student Success, built cross-campus collaborations with the UMass libraries and the English department; this increased the program’s reach (contacting students by email) and visibility (social media). Participation has increased each year, and they have moved away from prize incentives toward a pizza party (again, bringing people together).
- Veronica from the Boston Public Library talked about a number of reading challenges for adults: summer, winter, and year-long. The year-long challenge wasn’t as much of a success for BPL, but engagement with the winter (Jan-Feb) and summer (Jun-Aug) has been good. Bingo-style sheets include things other than “read a book” (e.g. learn something new about your neighborhood, listen to a new song, etc.). Reading challenges for adults bring new patrons into (or back to) the library, connect patrons with resources, encourage love of reading and support of the library, help patrons diversify their reading, offer opportunities to cross-promote other programming, engage staff, and are fun! They don’t use themes, but they do craft bingo items around book lists they make in advance, and they find newsletters a better way to communicate than social media.

- The Center for the Book uses a “12 months, 12 books” model for their challenge, and relies on public libraries and independent bookstores as partners to spread the word and promote the challenge. People can sign up online and track their reading; there is a monthly newsletter and monthly prize drawings, and two year-end celebrations (in Northampton and Boston).
Exhibit Hall Break! I chatted with vendors from Transparent Language (I’ve been doing their ASL for Librarians course, and it’s fantastic), MLS, NELA, and others. I checked with both Baker & Taylor and Ingram to see if they had new award posters, but they didn’t; I found some downloadable ones from Follett, though.
10am: “Banned in the USA: A History of Censorship, Book Bans, and First Amendment Freedoms,” Jocelyn Kennedy, Executive Director of the Farmington (CT) Libraries
- Jocelyn ran us through the history of censorship in the U.S., though she said that censorship has existed as long as the printed word, and even before: “We don’t like when other people say things that we don’t like.” A few keywords and cases to search if you’d like to learn more: First Amendment, Sedition Act, Tariff Act, obscenity laws, Anthony Comstock (grr. See: The Future of Another Timeline by Annalee Newitz), Title 18 of the Federal Criminal Code, Joseph McCarthy and HUAC, the Hayes Code, the Comics Code Authority, Miller v. California (1973), Island Trees Union Free School District v Pico (1982), ALA Office of Intellectual Freedom (OIF).

- Government censorship is only part of the picture; some industries and organizations self-censor, sometimes in order to prevent government censorship. (Think of those “parental advisory” stickers on music CDs, movie ratings, etc.)
- Book challenges from individuals and organized groups are on the rise in the past few years, but the Pico v. Island Trees case set the precedent that school boards can’t remove books from school library shelves just because they don’t like them. Jocelyn said, “It’s important to remember that it’s a very small group of people who are pressing for censorship and book bans [but] they’re very well organized.” The best thing you can do is make sure you have a strong collection development policy and a strong consideration policy, backed by procedure. (If your library doesn’t have these policies, or needs to update them, the MLS helpfully collects examples.) And, administrators need to support frontline workers.
11:10am: “Leading with Love: Celebrating Pride at Your Library,” Jenny Santomauro (Peabody Institute Library of Danvers), Taylor Silva (Fall River Public Library), Miz Diamond Wigfall (a.k.a. AJ)
- FRPL hosted its first Drag Storytime in 2019, and hundreds turned out: so many that they had to offer the program several times that day. They hosted drag storytime several more times, again with high attendance and support and minimal protests, but in December 2022 the program was interrupted by hate group NSC-131, which tried to prevent people from entering; police presence helped ensure that the event ran uninterrupted. After another successful drag storytime in January 2023, leadership made the decision to move the venue from the library to the town recreation department, citing staff safety concerns. However, drag storytimes and Pride events continue in Fall River with plenty of support. Taylor leveraged existing relationships with individuals in the community and community groups to gain support for LGBTQIA+ friendly events and to offer more, like day trips, movie nights, craft programs, and a D&D group.
- Jenny spoke about a drag makeup class for teens, offered in May before Pride one year. The class filled up just minutes after being posted online, but then attracted hateful comments and threats. They were “scared but determined….We didn’t want to kowtow to these hate groups…We wanted to show that the library was a strong ally.” Police took the threats seriously, and allies showed up to create a “wall of love.” At future LGBTQIA+ events, the library advertised to local groups and schools, only posting to social media immediately before the event. There is a “clear need and desire for queer programs” in Danvers, and more supporters show up in person than protestors do.
- Miz Diamond Wigfall echoed this sentiment, saying that “keyboard warriors” are active online but few show up in person. It’s also important to have all-ages queer programs and spaces, as so many queer spaces are 18+. Parents are grateful for their kids to have safe spaces.

12pm: “Landscape Ideas for Education, Engagement, and Climate Resilience,” Elena Zachary, Regenerative Design Group, Greenfield, MA
- Elena talked about climate change, and the effects it’s already having in New England, and different types and sizes of garden projects that can help mitigate extreme heat, drought, and extreme rainfall, flooding, and storms. It’s possible to reduce heat island effects through landscaping by planting shade trees, for example, or “pocket forests.”

- RDG works on other projects, such as creating rain gardens, accessible gardens, outdoor classrooms, educational gardens, pollinator gardens, bird-friendly gardens (better than bird feeders: you don’t have to worry about bears, or refilling the feeders), and historical and cultural heritage gardens.
- What can libraries do? (1) Add native perennial plants to existing landscapes; (2) Plant and manage chemical-free (no chemical fertilizers or plants treated with neonics); (3) Mow less, and less often, and participate in No Mow May; (4) Leave the leaves – rake them off lawns and into beds to insulate shrubs and perennials, especially as there is less snowfall; (5) Use rain gardens, swales, and vegetation to infiltrate water onsite and avoid runoff.
- What else? Engage the local community, find out what they want – benches for reading, a living seed library, plant exchanges, edible gardens? Use public land to set an example (good signage helps!) and educate people that they can transform their own spaces as well – every little bit helps.
- Available grants: ARSL Sustainable & Resilient New England Libraries, LSTA/MBLC Dig In.
2pm: “Martha’s Vineyard Land Transfers: Being an Ally to Indigenous Peoples and Beyond,” Kara Roselle Smith (Chappaquiddick Wampanoag)
 Kara spoke about her historical family connection to Martha’s Vineyard – which was inhabited by the Wampanoag people before First Contact, but is now inhabited by descendants of colonizers – and Indigenous efforts to regain land that was wrongfully taken from them: “The stealing of native land wasn’t just a one-time event…[it] continues to this day.”
Kara spoke about her historical family connection to Martha’s Vineyard – which was inhabited by the Wampanoag people before First Contact, but is now inhabited by descendants of colonizers – and Indigenous efforts to regain land that was wrongfully taken from them: “The stealing of native land wasn’t just a one-time event…[it] continues to this day.”- She showed a long clip from a TEDx Talk by Lyla June (Diné), “3000-Year-Old Solutions to Modern Problems,” in which June describes land management techniques that decenter humans and design for future generations. June explained that European colonizers misunderstood Indigenous land management practices – “living heirlooms” – and that Indigenous people are a “keystone species.”
 Kara recommended two books for further reading: This Land Is Their Land by David J. Silverman and We Talk, You Listen by Vine Deloria Jr. (I would add that another good book on this topic is Occupying Massachusetts by Sandra Matthews, David Brule, and Suzanne Gardinier.)
Kara recommended two books for further reading: This Land Is Their Land by David J. Silverman and We Talk, You Listen by Vine Deloria Jr. (I would add that another good book on this topic is Occupying Massachusetts by Sandra Matthews, David Brule, and Suzanne Gardinier.)
2:40pm: “Touchpoints in Libraries,” Lyndsay Forbes (MBLC) and Christi Farrar (MLS)
- The Touchpoints training program was developed by T. Berry Brazelton in 1995, originally designed for health care settings but adapted for libraries. Why Touchpoints in libraries? “It’s about family engagement.” Touchpoints is a systems approach, and libraries are part of a child’s system.
- Touchpoints is a way of addressing different perspectives and assumptions, recognizes our own biases, and moving from a deficit-based view to a strengths-based one. Library staff can change our interactions with patrons by understanding where we’re coming from and being good listeners.
- Starting in 2020, the MBLC and MLS began the process of going through the “train the trainer” program and offered the first trainings with two cohorts in 2023; another training will be offered this fall. Cohort learning creates a professional learning network, encourages reflective practice, and models relationship building.
3:30pm: “Our Grandest Challenge with The Sustainable Libraries Initiative,” Rebekkah Smith Aldrich, MLS, LEED AP
- “Even if we do everything right [climate-wise from here on], we have a minimum of another 30 years of increasingly severe and scary weather….It’s already here, it’s already impacting us.” The medical community is calling climate change the biggest threat to global public health: “The climate crisis will profoundly affect the health of every child alive today.” –The Lancet
 The ALA added Sustainability to its Core Values in 2019. That means it should be part of our framework for libraries’ decision-making. Look at the “triple bottom line” definition: environmentally sound, socially equitable, economically feasible (see graphic at right).
The ALA added Sustainability to its Core Values in 2019. That means it should be part of our framework for libraries’ decision-making. Look at the “triple bottom line” definition: environmentally sound, socially equitable, economically feasible (see graphic at right).- Librarians can align for collective impact, like the Blue Marble Librarians are doing. Project Drawdown is a good resource: “embrace the idea that every job is a climate job.” Libraries can do a lot to mitigate climate change – even small changes like using LED lights add up, and putting up solar panels is even better. Put EV charging stations in the library parking lot, and build net-zero goals into strategic plans, like Concord.
- Libraries are also important when it comes to disaster preparedness and community resilience. Communities with tighter social fabric will do better (see: Heat Wave by Eric Klinenberg). A few more resources and ideas:

- MBLC Library Building Programs: Sustainability & Resilience
- Find your FEMA Region (New England is Region 1)
- MA Climate Change Assessment (report with graphics)
- Libraries as Cooling Centers
- Communities Responding to Extreme Weather (CREW)
- Build community by establishing Library of Things collections (e.g. tools), creating gardens, hosting seed and plant exchanges, and bringing in repair cafes or fix-it clinics. Encourage young people who want to help Do Something.
Finally, Governor Maura Healey’s keynote speech was moved from the morning to the afternoon, to close out the day’s presentations. She quoted one of my all-time favorite library quotes, from Caitlin Moran’s essay “Alma Mater”:
A library in the middle of a community is a cross between an emergency exit, a life raft and a festival. They are cathedrals of the mind; hospitals of the soul; theme parks of the imagination….They are the only sheltered public spaces where you are not a consumer, but a citizen instead. -Caitlin Moran
Healey spoke generally of her childhood memories of libraries, and her support for intellectual freedom in Massachusetts. She mentioned the nationwide book banning trend and cited the challenge statistics from the ALA OIF, saying, “What a damaging and alarming trend. They want to remove books and programming that tell the truth….We are never ever gonna let that happen in Massachusetts. We cherish our libraries.” Healey acknowledged the link between libraries and democracy, and pledged support for library resources, including the economic development bill, which includes $150m for library construction grants.
People asked excellent questions during the Q&A: about Healey’s support for libraries in public schools (“If you could give this same talk to school superintendents…”), about how municipal employees aren’t covered by FMLA (she gave a weird answer about housing costs instead), about legislation to protect library collections (“I’m in favor of any legislation that would ban the banning of books”), and, of course, what she’s reading right now (Margaret Atwood essays, The Climate Book by Greta Thunberg, and Russell Banks’ last book).
And that was a wrap (for me, anyway) on MLA 2024! I’m going forward with new ideas about how to make the library more sustainable and resilient, host queer-friendly programs, and run reading challenges (the good kind, not the banning kind). Thanks so much to all the presenters and panelists, vendors, and conference committee!









 Well, I may not
Well, I may not 
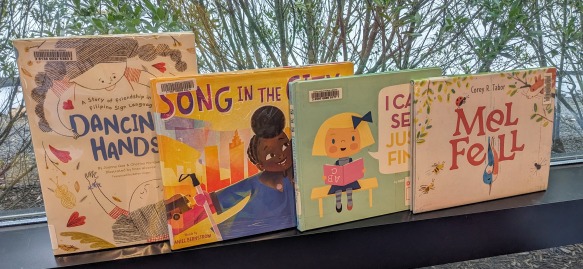
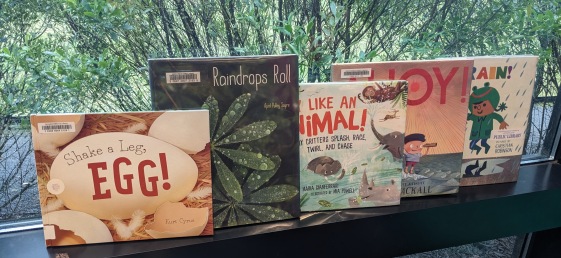
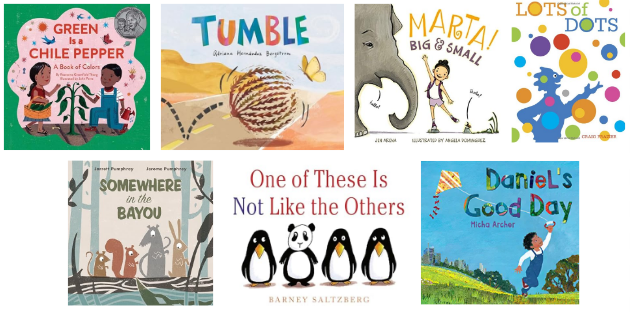
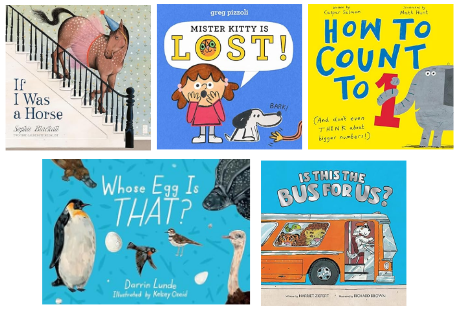
 All of these books, in their own way, are about ability. Perception and communication also emerge as themes.
All of these books, in their own way, are about ability. Perception and communication also emerge as themes. Song in the City is a little bit longer, but the illustrations are super bright – featuring that warm yellow from the cover – the text rhymes, and there are a lot of sound effects. This was definitely the book that the adults in the room loved best. We all paused in the middle to close or cover our eyes, as Emmalene helps Grandma Jean do in the book, to focus on what we could hear.
Song in the City is a little bit longer, but the illustrations are super bright – featuring that warm yellow from the cover – the text rhymes, and there are a lot of sound effects. This was definitely the book that the adults in the room loved best. We all paused in the middle to close or cover our eyes, as Emmalene helps Grandma Jean do in the book, to focus on what we could hear. I would love I Can See Just Fine based on its title alone, but the execution is just perfect. A little girl named Paige has trouble seeing the board at school, reading her sheet music, and even identifying animals (she picks up a skunk and calls it a kitty). She is not excited to go to the eye doctor, or when they tell her she needs glasses, but when she stands in front of the huge array of frames to choose from on the wall, you can just feel her wonder and awe. She tries on lots of frames and chooses the right ones for her. I showed the group my own glasses, identifying the different parts (frames and lenses). I also shared with the group that the eye doctor is my favorite one to go to – they never give shots!
I would love I Can See Just Fine based on its title alone, but the execution is just perfect. A little girl named Paige has trouble seeing the board at school, reading her sheet music, and even identifying animals (she picks up a skunk and calls it a kitty). She is not excited to go to the eye doctor, or when they tell her she needs glasses, but when she stands in front of the huge array of frames to choose from on the wall, you can just feel her wonder and awe. She tries on lots of frames and chooses the right ones for her. I showed the group my own glasses, identifying the different parts (frames and lenses). I also shared with the group that the eye doctor is my favorite one to go to – they never give shots! We wrapped up with Mel Fell, which is about confidence and ability in a different way: a baby kingfisher’s first flight/dive. The orientation of this book is unique (in the photo above, the spine is actually on top), and there’s a fun rotation required part of the way through the story. We see community members – other residents of Mel’s tree – attempt to help, but ultimately, Mel was right about their readiness to fly!
We wrapped up with Mel Fell, which is about confidence and ability in a different way: a baby kingfisher’s first flight/dive. The orientation of this book is unique (in the photo above, the spine is actually on top), and there’s a fun rotation required part of the way through the story. We see community members – other residents of Mel’s tree – attempt to help, but ultimately, Mel was right about their readiness to fly!
 (overlap with GN)
(overlap with GN)
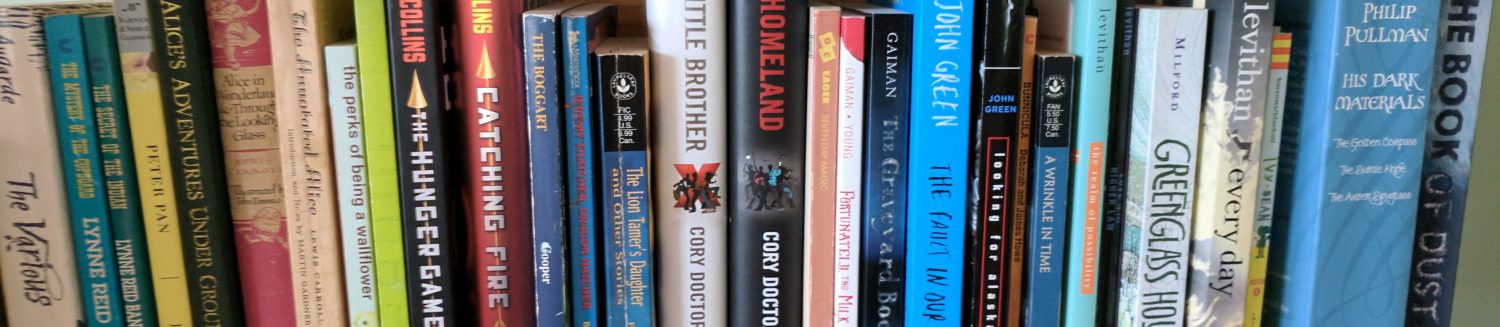
 Re-reads: Unknown; I don’t have a good way to keep track. The kiddo listened to all five Mysterious Benedict Society books for what felt like months, and we re-read all of the Dealing with Dragons books by Patricia C. Wrede. I re-read a chunk of Greenglass House by Kate Milford, as I always do toward the end of December, and I certainly revisited favorite picture books at home and at library storytimes. And, after reading Simon Sort of Says in March and refusing to shut up about it since, I re-read it as an audiobook this month and it’s still stunningly good.
Re-reads: Unknown; I don’t have a good way to keep track. The kiddo listened to all five Mysterious Benedict Society books for what felt like months, and we re-read all of the Dealing with Dragons books by Patricia C. Wrede. I re-read a chunk of Greenglass House by Kate Milford, as I always do toward the end of December, and I certainly revisited favorite picture books at home and at library storytimes. And, after reading Simon Sort of Says in March and refusing to shut up about it since, I re-read it as an audiobook this month and it’s still stunningly good.